How to install Magento security patches |
|
by David Dwyer on 28/01/2019 |
Are your security patches up to date?Is your e-commerce store secure? It is essential to update and maintain online store security to avoid data being compromised.
Often e-commerce stores are managed by an administrator without the necessary programming, security or personal data usage per General Data Protection Regulation knowledge.
For the purposes of this article we will look to cover Security. Further we will always recommend having professionals maintain your platform to ensure your security is kept up-to-date.
To be clear too, the comfort an up to date security version means is that the bar is higher it does not mean it cannot be breached (just that it is much harder to breach, see recent instances from British Airways which demonstrate this perfectly). That said it can mean the difference between business success and failure for your e-commerce store.
What is the process to install Magento security patches? This article details the process to install security patches in a Magento Commerce 1.9.x store.
The software company regularly publishes patches to resolve platform vulnerability errors, as well as updates to services such as PayPal or shipping methods. However, business owners, perhaps like you are not only responsible but very much accountable for applying these patches.
Are your security patches up to date? To start you need to determine if your security patches are up to date. If you don’t know, that probably means you aren’t up to date, unless of course you have only just installed the latest version.
If unsure, visit MageReport, a free service that provides an overview of the security status of your Magento shop including suggestions to manage vulnerabilities.
Be aware however, it’s not 100% dependable. Often the site is not able to detect all the different types of patches nonetheless it will provide a starting point for those it can identify so you know they are installed.
For information about which patches have been applied, open your Magento install directory /app/etc/applied.patches.list
Whenever a security patch is installed using the command line, an entry is created in this file so you can check which patches were previously installed. When you get to this point you will come across one of the following;
I don't have the applied patches file If the file doesn’t exist, it means that patches have never been installed using the command line. In this case, you will need to find out what patches have been installed by taking the following steps;
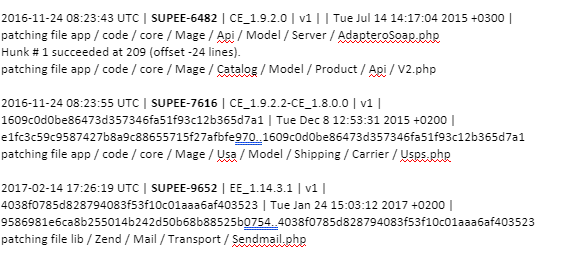
Yes, the applied patches file exists If you can see the applied patches file, open it and it will detail the information required. For example;
The information will include the patch identifier and the installation date. If the file information is in chronological order simply take note of the last patch in the file and then go to Magento downloads
In the above example you would search for SUPEE-9652 and read the description, this is important. Information about patch updates, obsolete patches and replacements are detailed here. Take note because this will save you time and work reinstalling patches.
In this case the patch SUPEE-9767 patch is deprecated, and the instruction is to install the SUPEE-9767 v2 patch instead.
I have the applied patches file, now what? If you have the applied patches file related to your security patch, install it.
The only other necessity is having access to your server's root directory. To do this, upload the patch to your server and execute the following command from a ssh terminal:
sh filename
You will get one of the following messages; Message 1 This means the patch has been installed correctly however please do not be disheartened if this message does not appear.
Message 2 This means you could not install the patch.
Help Never fear if the patch doesn’t install, there is a solution. The install may have been unsuccessful because the Magento patch file has changed or the base code has been modified. This can happen due to developer error or because the file is from a different Magento version than what has been indicated in the patch.
However, the answer will be right in front of you. The error message will tell you which file/s are the problem and in which line to find the error. This means a manual patch can be made.
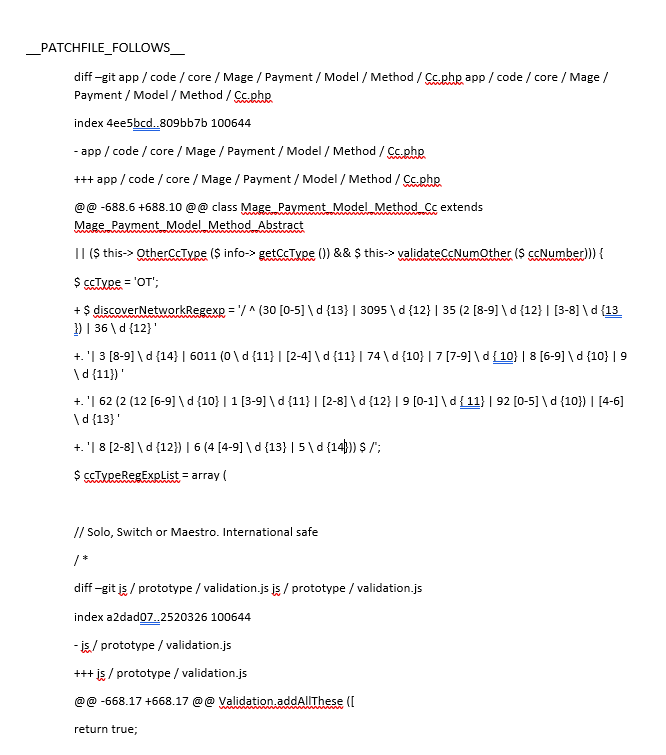
Open the patch file with a text editor to identify the error. Modifications to a file will always start with;
diff - -git
Here is the file to modify. The lines that start with @@ indicate the line of the file to look for.
Using the example;
Hopefully, the problem is only a line break, so deleting it will correct the file and therefore the patch. Run the patch again to see if there are any problems.
If there is still an error, it means the file has modifications to the code so it will never match. In this case, patch modifications will need to be made manually.
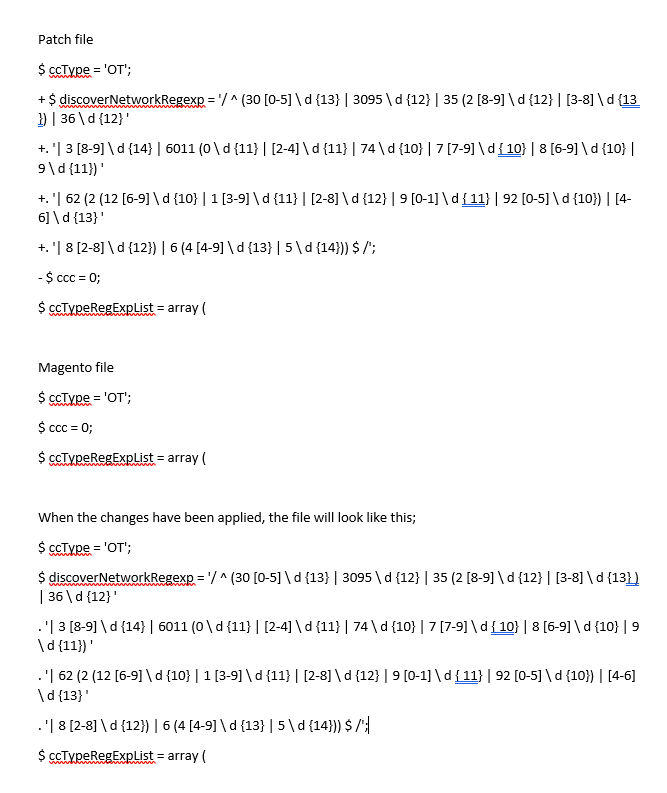
Installing a patch manually To manually install a patch, open the patch file with a text editor.
Lines that start with a + are lines to add to the Magento file and those that start with a - are to be deleted.
It is necessary to identify which section of the code to insert and remove lines. To achieve this, the patch file will have provided you with a few lines of code before and after the modification, so you can easily locate it. For example;
Now that the file is updated, proceed to delete the piece of code from the patch file, highlighted in red. This will ensure you do not try to update it when running the patch file again.
Save the file and run it again via your console. If errors reappear, repeat the previous step.
When no errors are detected, Magento will patch all the files that do not identify problems and proceed to update the file /app/etc/applied.patches.list
A note This guide has been prepared for the technical savvy. It is not recommended to perform any of the above steps if you don’t know what you are doing. If you need assistance, contact Developer SOS. Our team of professionals specialise in Magento and will be able to perform these and other tasks for you. |
|
Cyber Security, Cyber Security Vulnerabilities, Developer SOS, e-commerce, e-tailers, Magento 1.9.x, Magento 2.x.x, Magento e-commerce, Online Stores, Security, Web Consultancy, Web Design, Website Support, Website Vulnerabilities
|
|
|